Secure Your Account with Two-Factor Authentication
Traditional usernames and passwords are no longer enough to protect your business from cyber threats. Phishers, malware, or even simple human error can steal passwords. Two-Factor Authentication (2FA) adds an extra layer of protection. It makes it much harder for attackers to access your data and systems.
While some may see 2FA as an extra step, it is now essential in today’s digital world.
It helps secure business accounts, sensitive data, and remote access systems.
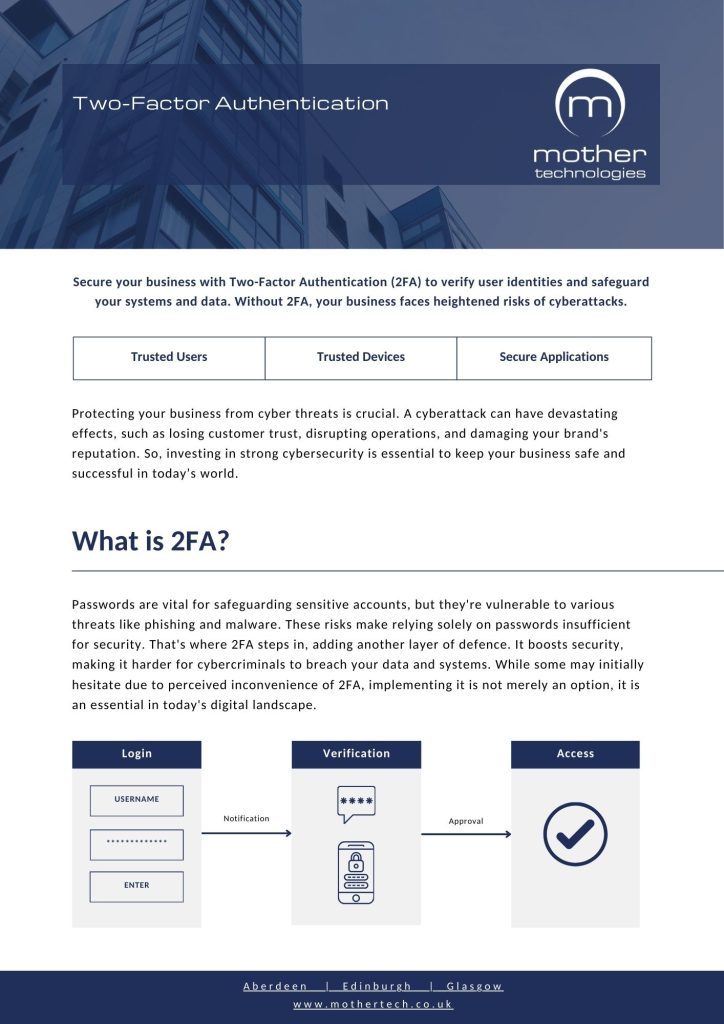

Two-Factor Authentication, or 2FA, requires users to provide two types of verification before they can access an account. The first factor is something you know, such as your password. The second factor is something you have, like a code sent to your phone or generated by an app.
Even if someone steals your password, 2FA makes it extremely difficult for them to break into your accounts. It’s one of the most effective ways to protect against unauthorised access and data breaches.
There are several ways to implement two-factor authentication, depending on your business needs:
An authenticator app helps verify your identity in a secure way. It can generate a time-based code on your phone. It can also send a prompt that you approve in the app. This method stays highly secure because your device performs the verification and attackers cannot easily intercept it.
A one-time password (OTP) is sent via text message to your phone. It’s simple to use and widely adopted, but slightly less secure than an authenticator app.
A code or verification link is sent to your email address. While it is easy to set up, email-based 2FA is less secure.
We recommend using it with other methods for stronger security.
When it comes to securing your business, Duo two factor authentication is the solution we recommend. It’s reliable, easy to use, and designed with real teams in mind. If you’re looking for a trusted, modern authentication service that just works, Duo is our go-to choice.
Reduces the risk of cybercriminals breaking into your accounts.
Protects against phishing, credential theft, and brute-force attacks.
Helps meet cybersecurity and data protection requirements.
Works with cloud platforms, VPNs, and remote access tools.
Minimal disruption to users while greatly improving security.
